So difficult it is to show the various meanings and imperfections of words when we have nothing else but words to do it with.
—John Locke
Introduction
In today’s rapidly evolving digital landscape, I cannot overstate the importance of robust enterprise cyber risk management (ECRM). As cyber threats become increasingly sophisticated, understanding and effectively managing these risks are paramount for organizations aiming to protect their assets, maintain trust, and create value.
From my previous writings, you know that I believe risk illiteracy is one of the three root causes of our veritable cyber risk management mess. See my four-part series starting with Cyber Risk Illiteracy – 1 – Stomp Out Risk Illiteracy.
This article briefly defines basic, critical concepts and explains why these concepts are essential to an organization’s cybersecurity strategy. Below is a summary of these key terms and their significance.
Risk
At the heart of ECRM is the concept of risk. The Committee of Sponsoring Organizations of the Treadway Commission (COSO) defines risk as “the possibility that events will occur and affect the achievement of strategy and business objectives.” This definition is crucial because it emphasizes that risk is not inherently harmful; it can also present opportunities. For instance, managing cyber risks effectively can lead to increased market trust, operational efficiencies, and competitive advantages.
In contrast, the National Institute of Standards and Technology (NIST) defines risk with a focus on potential threats and adverse outcomes. This perspective is equally important as it underscores the need for vigilance and preparedness against harmful cyber events. I suggest adopting a balanced approach, viewing risk as both a possible bad thing (i.e., a risk) and a potential good thing (i.e., an opportunity). This dual perspective is vital for developing a proactive and comprehensive ECRM program.
Risk Owner/Executive
A critical aspect of effective ECRM is clear ownership of cyber risks and opportunities. Organizations must avoid the outdated notion that the IT department or Chief Information Security Officer (CISO) is solely responsible for these risks. Instead, I advocate for assigning risk ownership to business process owners, department managers, and organizational functional leaders. In other words, not the IT or security team. This decentralized approach ensures that cyber risks are managed where they are most impactful—within the specific business units that rely on the associated information assets.
NIST defines a risk executive as an individual or group responsible for ensuring that security risks are managed from an organization-wide perspective. This role is crucial for maintaining consistency in organizational risk management practices and aligning them with strategic objectives.
Risk Management
Risk management involves the coordinated activities to plan, direct, control, and make decisions concerning the effects of uncertainty on objectives. This definition, adapted from ISO Guide 31000:2018, emphasizes that uncertainty can lead to positive and negative outcomes. In the context of ECRM, risk management is about more than just mitigating threats; it also involves identifying and capitalizing on opportunities that can drive business growth and enhance competitive positioning.
Effective risk management requires a holistic approach considering all types of risks—strategic, financial, regulatory, operational, legal, and cyber. For cyber risks, this means integrating cybersecurity measures into the broader enterprise risk management (ERM) framework to ensure comprehensive protection and value creation.
Enterprise Risk Management (ERM)
Enterprise Risk Management (ERM) is a holistic process for identifying, assessing, and managing risks that could interfere with achieving corporate objectives. ERM typically focuses on managing the downside, such as regulatory compliance and implementing controls to mitigate risks. However, I encourage a broader view that includes managing the upside—leveraging risks as opportunities for innovation and value creation.
This expanded view of ERM is essential for organizations aiming to use cybersecurity as a defensive mechanism AND strategic enabler. By integrating ECRM into the overall ERM program, organizations can better align their cybersecurity efforts with their business goals and create a more resilient and agile enterprise.
Enterprise Cyber Risk Management (ECRM)
ECRM is a specific aspect of ERM that deals with cyber risks and opportunities. Cyber risk management cannot be isolated from an organization’s overall risk management efforts. Cyber risks have the potential to impact every stakeholder, from consumers to business partners, and can affect an organization’s ability to achieve its strategic objectives.
ECRM is not just about protecting against cyber threats; it also involves identifying and pursuing opportunities to create business value. This dual focus makes ECRM a critical component of any organization’s risk management strategy, as it ensures that cybersecurity efforts are aligned with broader business goals and can contribute to long-term success.
Cybersecurity
Cybersecurity is defined as the ability to protect or defend the use of cyberspace from cyberattacks. This defense includes safeguarding data, systems, and devices’ confidentiality, integrity, and availability (CIA) against anticipated threats and vulnerabilities. A strong cybersecurity strategy is a foundational element of ECRM, essential for maintaining trust and operational continuity in the digital age.
However, cybersecurity should not be viewed solely as a defensive measure. A well-developed cybersecurity strategy can also enable business growth by protecting intellectual property, enhancing customer trust, and supporting digital transformation initiatives.
Strategy
Strategy is a critical component of board oversight and involves creating economic value by gaining a competitive advantage through a unique value proposition. In the context of cybersecurity, this means developing a strategy that not only protects the organization from cyber threats but also enables it to leverage cybersecurity as a business enabler and value driver.
A successful cybersecurity strategy must align with the organization’s vision, mission, and values and be integrated into the overall ECRM program. This alignment ensures that cybersecurity efforts are not just reactive but are part of a proactive approach to managing risks and opportunities in a way that supports the organization’s strategic objectives.
Cybersecurity Strategy
The cybersecurity strategy outlined in my book, Enterprise Cyber Risk Management as A Value Creator | Leverage Cybersecurity for Competitive Advantage, is driven by and aligned with the organization’s broader strategic goals. It involves identifying and prioritizing cyber risks and opportunities, implementing appropriate security measures, and fostering a culture of continuous improvement and adaptation.
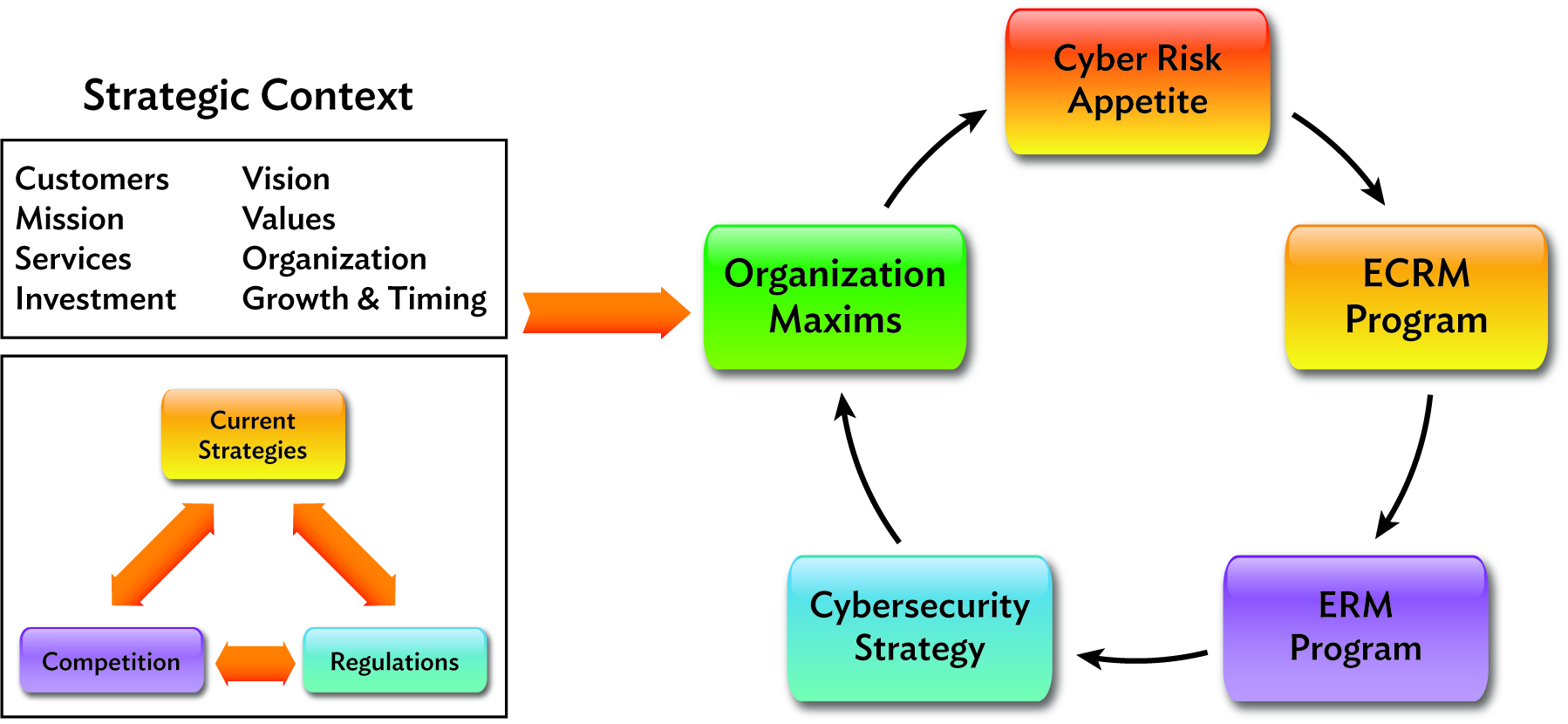
In my book, I present a model for aligning ECRM, ERM, and cybersecurity strategy, illustrating how these elements work together to create a comprehensive approach to managing cyber risks and leveraging opportunities. This integrated approach is essential for organizations that want to stay ahead of emerging threats and use cybersecurity as a tool for competitive advantage.
Conclusion
Understanding and effectively managing the key terms discussed in this article—risk, risk ownership, risk management, ERM, ECRM, cybersecurity, strategy, and cybersecurity strategy—are crucial for any organization seeking to thrive in today’s digital landscape. By adopting a holistic and proactive approach to ECRM, organizations can protect themselves from cyber threats AND leverage cybersecurity as a strategic enabler for growth and value creation.
This article provides some key ECRM definitions. To learn more, including an entire appendix, Twenty-Five Essential Terms for Your ECRM Glossary, order your copy of Enterprise Cyber Risk Management as A Value Creator today.